Enables SecOps teams to automate management of the entire security policy life-cycle with dramatic reduction in change request response time.
Use Case
SECURITY COMPLIANCE & FIREWALL ORCHESTRATION

IT Security Orchestration
Powered by StackStorm
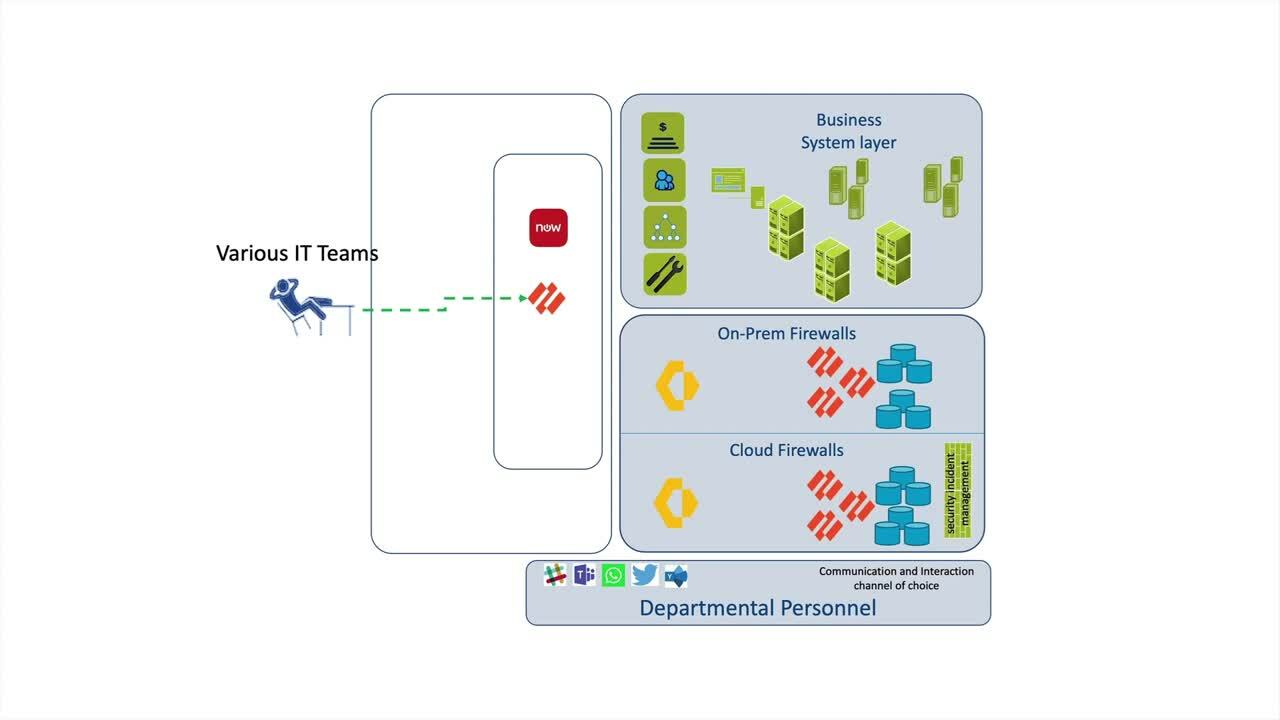
Situation: Manual Compliance & Firewall Orchestration
- Without automated security policy compliance management in place all security policy change requests require manual human intervention.
- A user request to update a security policy creates a ServiceNow (or similar ITSM) ticket, specifying the target security policy and the changes to be made.
A member of the SecOps team manually reviews and takes action on the requested changes. This involves checking the policy changes to ensure they have been defined correctly and are not in conflict with other policies.
- The ITSM ticket is then updated and closed. Although this process is well-understood, it is inefficient and prone to human error that can result in disruption or downtime.
Manual Compliance & Firewall Orchestration
The Conventional Workflow Approach
Manual Process: 2-4 Stressful Hours for Network Operations (see Figure 1 below).
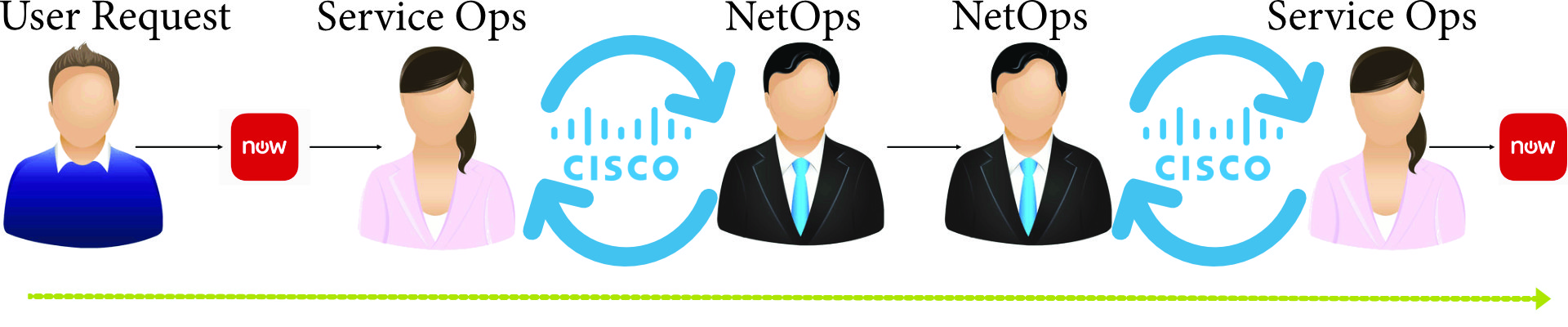
A user recognizes that a service has gone down and creates a ServiceNow ticket. Service Ops assigns the ticket to NetOps with a Priority 1.
NetOps team members now manually start diagnostics, discovering that an interface is down. Remediation action is performed to bring up the interface.
NetOps team now either updates the ticket if successful or continues running diagnostics to discover why the interface went down, staying as a priority level 1 task. The ServiceNow record is then updated and closed.
Figure 1 – Manual Interface Outage Response
Orchestral.ai's Composer Solution
Composer provides out-of-the-box integration with hundreds of tools, apps, devices and services used in SecOps environments. With the addition of Composer’s event-driven architecture, security policy change requests can be validated automatically. Composer then orchestrates a cascade of changes across the security infrastructure to ensure end-to-end configuration accuracy and policy compliance. Composer can also perform firewall CRUD operations and integrate with security policy management tools, enabling SecOps teams to easily create complex cross-domain workflows that reduce both the risk of disruption and the response time for change requests.
Maestro + Composer: 20-40 Stress Free Seconds (see Figure 2 below).
Automated Security Compliance & Firewall Orchestration
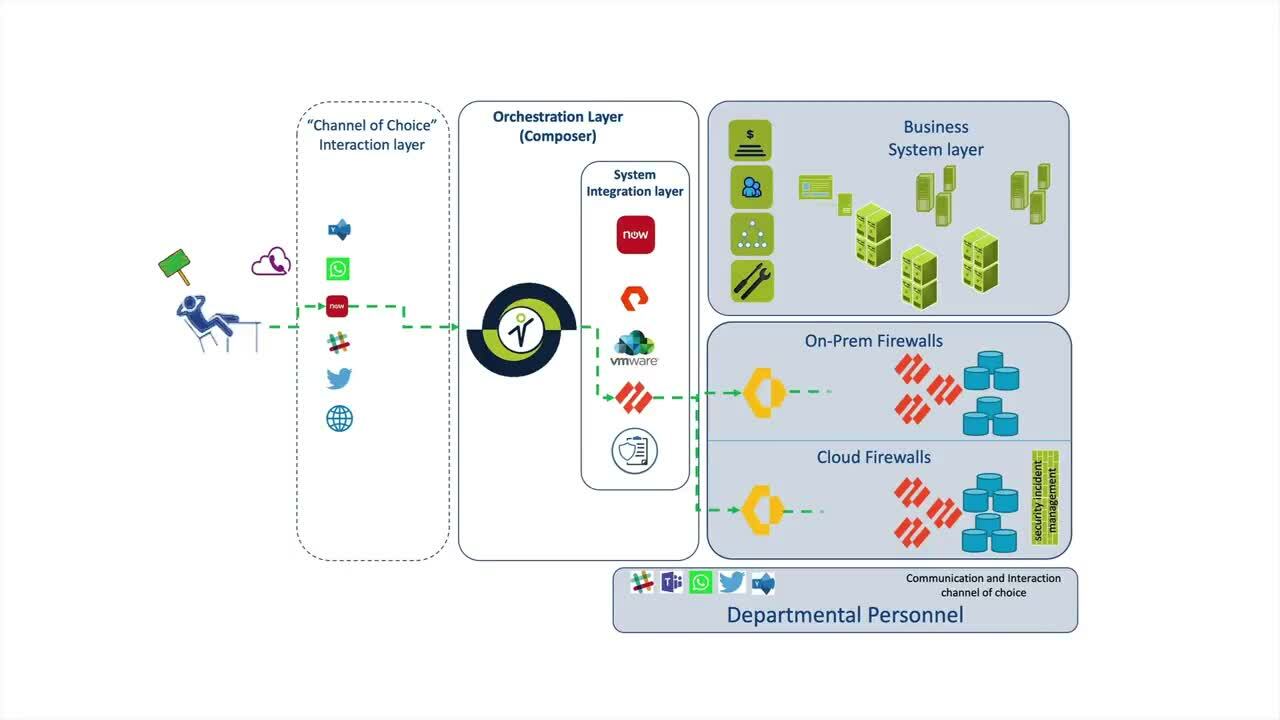
Figure 2 – Maestro + Composer Automated Event Driven Network Remediation
Composer Security Automation & Orchestration
- With the addition of Composer’s event-driven architecture, security policy change requests can be validated and implemented automatically.
- For example, an operator can initiate a change request with Composer directly or they can do so with an ITSM ticket that triggers a Composer workflow.
- And, once validated, Composer orchestrates a cascade or changes across the security infrastructure to ensure the end-to-end configuration is accurate and policy compliant.
- Next, Composer will ensure that the validated and implemented changes are synchronized with the appropriate security policy management tool.
- Composer will then reconcile the ITSM ticket corresponding to the change request and notify the SecOps team so they are aware that the change request has been successfully implemented.
- With Composer, SecOps teams can automate management of the security policy change life-cycle, with a dramatic reduction in the response time for change requests while minimizing the risk of disruption due to conflicting or non-compliant changes.
Composer Benefits
Automates Policy Management
Ensures Change Request Compliance
Minimizes manual intervention to ensure change request compliance while providing a clear audit trail for timely remediation when required.
Reduces Risk of Disruption/Downtime
SecOps teams reduce the risk of downtime or disruption due to conflicting or non-compliant changes.
Getting Started
Orchestral's solutions are available as free 30-day Proof of Value evaluations. To get started, just click the "FREE TRIAL" button at the top of this page and complete the Trial Request Form. If you'd like to see a demo first, just click the "Book a Demo" button below to book a date/time that works best for you. Otherwise, you can get started by emailing us at info@orchestral.ai.
Ready to see for yourself?
We'd love to show you how Orchestral.ai enables you to address a broad spectrum of orchestration & automation challenges.
Book a Demo